The Nauseating Truth About FIN12 for Hospital CISOs
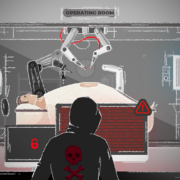
FIN12’s Ruthless Tactics Put Lives at Risk
FIN12 is an aggressive, ransomware-focused cybercrime group that specializes in targeted attacks on the healthcare sector. While many cybercrime groups will avoid hospitals, nursing homes, and 911 services — FIN12 has no reluctance.
Since 2018, FIN12 has actively targeted a range of businesses — making the group one of the most notorious big game hunters in cybercrime. Nearly 20% of their victims are in healthcare; 85% are in North America; and all boast revenues of at least $300 million. With no sign of remorse or morals, FIN12 stands in stark contrast to other cybercriminals: DoppelPaymer and Maze claim that they provide free decryption keys if they accidentally target a vulnerable group. FIN12 deliberately seeks them out.
A New Challenge For Hospital CISOs
No sector is safe from this group’s reach (they have also attacked government websites, schools, universities, and local municipalities), but their ruthless tactics pose a huge threat to healthcare. CISOs have to strategize for FIN12’s attacks — especially if long-distance treatments like telesurgery become more prominent, which will raise the stakes astronomically.
FIN12’s Brutal Methods
FIN12’s single-minded focus on ransomware deployment sets them apart. Their methods are ruthless — and brutally quick. By developing close partnerships with other threat actors who have already gained access to a victim’s network, FIN12 can creep in undetected and quickly deploy debilitating ransomware. Then, when access is securely locked down, they request a single large payout in Bitcoin. Their time-to-ransom (TTR) is incredibly short — the attack and payout all occur in 2 to 3 days.
To make their attacks more complex, FIN12 often overlaps toolsets and services to include backdoors, droppers, and codesigning certificates. The rise of remote work and relaxed home cybersecurity has made it easier for them to access remote logins — paving the way for their attacks.
A Reason to Pay Ransom
FIN12 is in it for the money — not for the data. Since they solely encrypt or block access to data instead of exfiltrating it, there’s an incentive for hospitals to pay up, get systems running, and save lives. Without the threat of corrupted data or exposed personal identifiable information (PII), their victims have reason to believe that they won’t be extorted or left behind without restored access. Additionally, FIN12 has a reputation for taking payment and moving on — another reason used to justify random payments.
A Stronger Defense
Along with updating security processes, procedures, and systems — the no-brainer basics — educating healthcare personnel on cyber security best practices helps prevent attackers like FIN12 from gaining a foothold. In most cases, mismanaged credentials and privileges lead to a breach: Many successful attacks began with a mere phishing email.
Enacting safety standards such as prohibiting personal use of company devices, using multi-factor or adaptive authentication, and keeping OS and antivirus software up to date can go a long way in preventing threats from getting in.