Product
Reveal Hidden Behavioral Intent
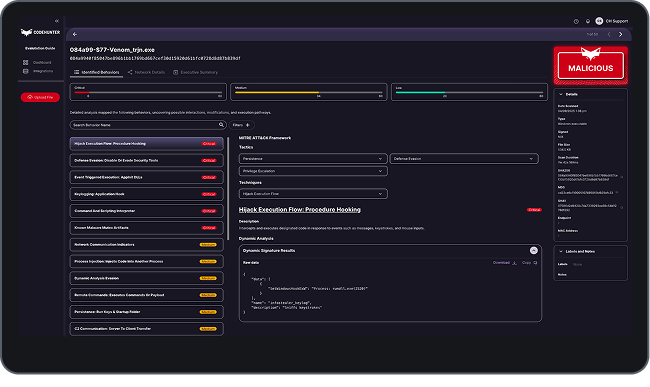
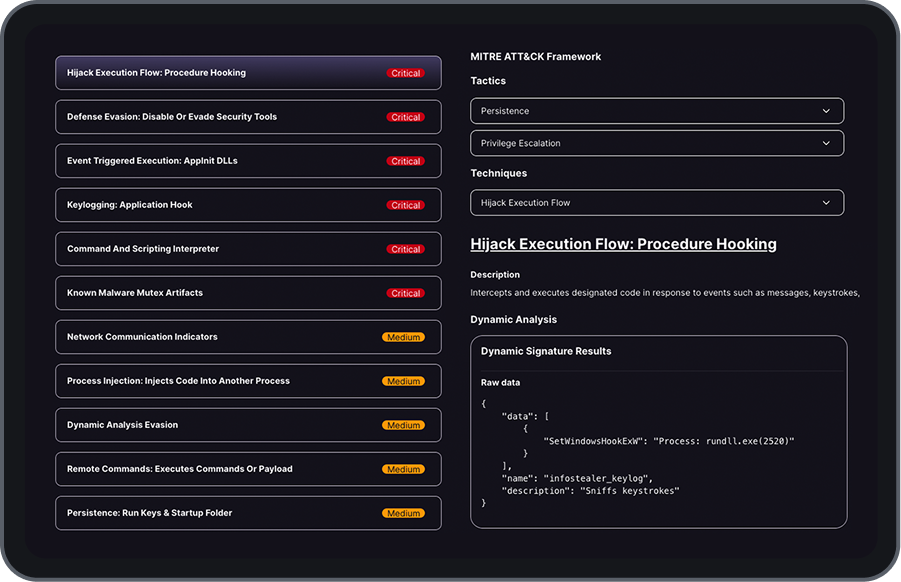
Identify the true intent of software artifacts before they enter your infrastructure. By analyzing execution patterns and behavioral indicators pre-runtime, we provide a definitive look at the actions code is programmed to perform, ensuring only verified, trusted code is allowed to run within your environment.
Enforce Deterministic Trust Decisions
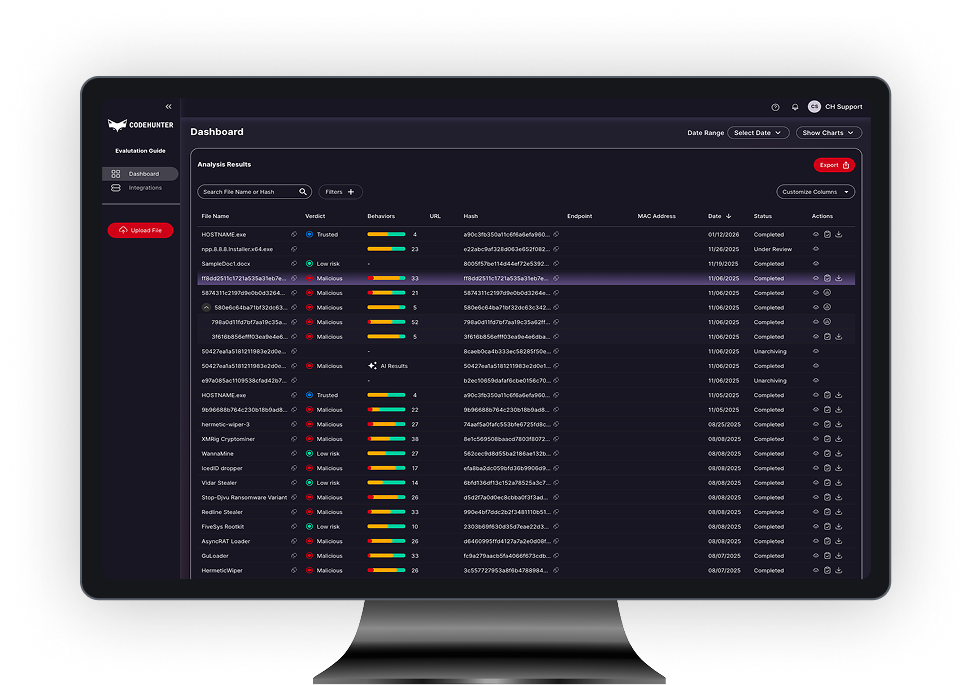
Move beyond the uncertainty of probabilistic scoring. We provide the deterministic evidence needed to drive immediate action to allow, block, or escalate threats—ensuring your response is always based on verified behavioral intent.
Automate Forensic Reverse Engineering
High-volume artifact analysis shouldn’t stall your operations. We automate the malware reverse engineering process to reveal malicious intent in seconds, replacing the slow, resource-heavy nature of traditional sandboxing with rapid, deterministic insights.
Standardize Threat Intelligence Mapping
Convert technical forensics into actionable intelligence instantly. CodeHunter automatically maps observed behaviors to the MITRE ATT&CK framework, providing your SOC with the immediate context needed for standardized response and governance across the enterprise.
Unified Guardrails for Code Execution
Enforce Zero Trust for Code across your enterprise. By protecting key entry points—from endpoints to automation workflows—we provide a continuous, machine-speed security gate that verifies the intent of every artifact before it executes.
Strategic Risk Intelligence for Leadership
Translate complex behavioral data into executive-level clarity. We provide a unified view of software integrity, offering CISOs real-time dashboards and audit-ready evidence to satisfy NIST and SOC2 compliance requirements with absolute certainty.